Bypass CAPTCHA: How Proxies Can Help

CAPTCHA stands for Completely Automated Public Turing test to tell Computers and Humans Apart, and every Internet user has seen it at least once. While it’s a robust cybersecurity tool that prevents website abuse, it can disrupt business activities, such as data scraping or account management. Here, let’s explore how CAPTCHA works and how one can bypass it for legitimate business purposes using proxies and antidetect browsers.
How does CAPTCHA work
Although called a Public Turing test, CAPTCHA is actually the inverse of a Turing test. It asks whether the visitor claiming to be human is, in fact, a bot. The system assigns a brief cognitive or visual task, exploiting known limitations in machine perception and pattern recognition
CAPTCHA types and trends
It’s essential to understand that CAPTCHA evolves along with the automated systems designed to solve it and automate website access. An example of the old-fashioned CAPTCHA that requires distorted-word recognition is shown below. For now, it’s almost meaningless: with modern optical character recognition (OCR) technologies, more than 50% of bot traffic passes these challenges with ease.
In 2009, Google’s CAPTCHA implementation, reCAPTCHA, was acquired from Carnegie Mellon University, and since then, it has become the gold standard, with ~85% market share as of 2026. While other services, like Cloudflare Turnstile and hCaptcha, challenge its dominance, let’s explore the typical examples of reCAPTCHA below.
v1 (legacy): Classic distorted-text challenge. Served a dual purpose: verify humans and help digitize scanned books by having users transcribe words that OCR couldn't read
v2 (checkbox): The familiar "I'm not a robot" tick box. It runs behavioral analysis of mouse movements, click rhythm, and browser history, and suspicious sessions get an image puzzle
v2 (invisible): No interaction needed at all for most users; the challenge only appears when risk signals spike and most resources are used to analyze sessions and fingerprints.
v3 (score-based): Runs entirely in the background, assigning a continuous risk score from 0.0 (bot) to 1.0 (human) based on behavioral signals like typing cadence, scroll patterns, and fingerprints. The site owner can decide which score threshold triggers a block or extra challenge.
reCAPTCHA Enterprise is a higher-tier version for banking, healthcare, and other privacy-sensitive enterprises, with deeper Google Cloud integration and highly customizable security policies.
While reCAPTCHA v1 is a weak protection as of 2026, reCAPTCHA v3 is quite effective at filtering traffic and can be customized to adjust the bot presence on the website based on conditions.
What does it mean to bypass CAPTCHA?
Or, in other words, what should be done to ensure that your browser activity will raise the minimum suspicions to the website’s automated anti-bot and anti-spam defences? Actually, there are very specific triggers that cause CAPTCHA to emerge, and you might even recognize them in your previous web surfing.
Suspicious IP address: A sudden traffic spike from one IP, or IPs associated with known proxy/VPN/datacenter traffic
No browsing history: A session with zero prior navigation on the site before hitting a sensitive action will be challenged almost certainly
Fingerprint anomalies: inconsistencies between declared browser headers and actual rendering environment
Rapid and repetitive actions, such as repetitive clicking and large data submissions in short windows
Other bot-like interaction patterns, including actions executed at perfectly uniform speed with no mouse movement variance
Modern CAPTCHA versions, such as reCAPTCHA v3, are effective against DDoS attacks and other malicious activities, as they evaluate incoming requests on various parameters and block suspicious ones.
Why to bypass CAPTCHA
CAPTCHA exists to protect websites from illegitimate activities, such as DDoS attacks and spam, but it can also disrupt legitimate business processes, including data collection and analysis. That’s why we need to understand how it can be avoided.
Do you want to ensure that your activities are legitimate? Learn about legal aspects of using proxies in CyberYozh!
How to avoid CAPTCHA: Best practices
Now, let’s explore what one needs to do to bypass CAPTCHA and build efficient web workflows.
Proxy usage: Account IP separation
Proxies are primary tools to bypass CAPTCHA and set up a virtual environment that won’t be challenged, but it’s essential to select the right proxy type and organize your Internet sessions in the right way. Let’s see how to do that.
Check the IP address health and trustworthiness before usage with CyberYozh’s IP Checker tool
First, you have to select a proxy type.
Residential proxies are assigned by real ISPs to real households, carrying high trust scores that defeat basic IP reputation filters. They’re good to use in most cases.
Mobile proxies are even harder to flag, as mobile networks use CGNAT, meaning many real users share the same IP range. Use them for social network activities.
Datacenter IPs are fast and cheap, but are easily identified as non-human and blocked by platforms like Cloudflare and Amazon. They’re acceptable for open database scraping.
After that, make sure to synchronize your perceived geolocation with the proxy IP’s location, as inconsistencies will likely trigger CAPTCHA challenges. Use IP rotation to distribute the request load across multiple IPs, and make sure each of your IP addresses is used for legitimate purposes so they aren’t flagged and their trust score isn't reduced.
Read more about proxy lifecycle to understand how IPs become flagged as “bad” and limited by platforms.
Antidetect browser: The next level
Proxies mask your IP and allow you to manage multiple accounts and send multiple requests with different IPs, but they don’t mask your digital fingerprints, which include system settings, hardware drivers, and browser data. To further enhance web surfing, antidetect browsers allow the creation of digital identities with unique fingerprint sets, and each of them can also be supplied by a proxy.
Read more about antidetection in CyberYozh’s article.
Antidetect browsers generate unique, synthetic browser fingerprints for each profile, making every session appear as a distinct human user to bot-detection engines. To be specific, they usually modify:
Canvas and WebGL hashes (GPU-level rendering fingerprints)
User-Agent string and browser version
Timezone, language, and locale
Screen resolution and color depth
Installed fonts and plugin lists
WebRTC IP leak masking
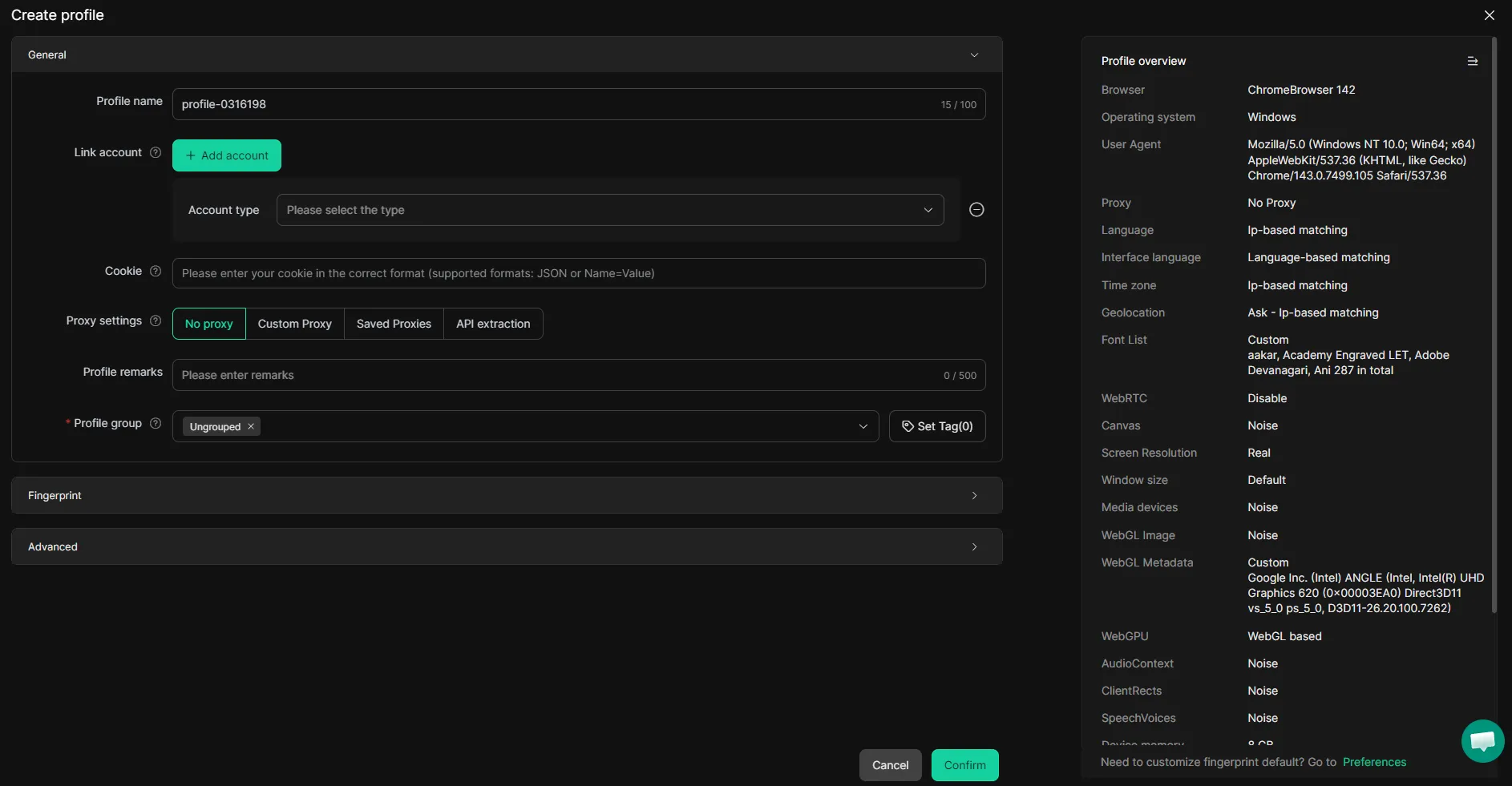
When antidetect browsers are paired with CyberYozh’s proxies, the profile becomes indistinguishable from a genuine user. Explore CyberYozh guides for setting up a proxy in Vision, DICloak, MoreLogin, and other antidetect browsers.
Automation tools: Scaling up CAPTCHA solving
Web automation tools, such as Playwright, Puppeteer, and Selenium, can help further optimize CAPTCHA solving. They integrate with antidetects and proxies, and can be used to automate and scale basic activities from mouse point movements and clicks.
Explore how exactly platforms detect unnatural activities in CyberYozh’s article about digital footprints.
With the right settings, these automated activities are performed in a way that doesn't trigger CAPTCHA. Examples are:
Add randomized delays between actions (50–300ms)
Simulate curved mouse movements and variable scroll speeds
Navigate across multiple pages before hitting the target
Accept and maintain cookies across sessions without overlaps between them
Set realistic viewport sizes and language headers
In that way, proxies, integrated into antidetect browsers and automated by tools like Playwright, can be used for efficient account management, post writing, form-filling, data scraping, app testing, and other business processes.
Proxy for CAPTCHA bypass: Specific use cases
Users need CAPTCHA bypass services for different activities, but some services are particularly popular. Let’s explore them shortly.
Amazon CAPTCHA bypass
Amazon is the world's largest e-commerce marketplace, making it a prime target for price monitoring, competitor research, and inventory tracking at scale. Its AWS WAF system deploys image-based CAPTCHAs, behavioral fingerprinting, and aggressive IP reputation checks that block scrapers within just a few requests. Businesses overcome this by combining rotating residential proxies with stealth-configured Puppeteer or BrowserQL, session cookie reuse, and third-party CAPTCHA solvers like 2Captcha. This stack allows continuous data extraction while maintaining the appearance of genuine returning shoppers.
Roblox CAPTCHA bypass
Roblox is a massive gaming platform where businesses and developers automate account creation, build bot-driven in-game economies, and test game mechanics at scale. It uses Arkose Labs' FunCaptcha, a 3D puzzle system that tracks mouse movement, click speed, and device fingerprints, making simple browser extensions completely ineffective. Automation teams use residential mobile proxies, paired with specialized FunCaptcha-solving APIs and human-behavior simulation scripts, to overcome these challenges. Clean, ISP-assigned IPs are critical, as Roblox instantly flags datacenter and free VPN addresses.
GitHub CAPTCHA bypass
GitHub is the leading code repository platform, where businesses automate CI/CD pipelines, scrape repository data for market intelligence, and manage multiple developer accounts. Its reCAPTCHA triggers activate during mass account creation, automated sign-ins, and high-frequency API interactions that deviate from standard human usage patterns. Developers bypass these challenges by integrating Google reCAPTCHA solver libraries with rotating residential IPv6 proxies offering per-request rotation and sticky sessions. Maintaining consistent session cookies per account profile is essential to avoid re-triggering verification.
Reddit CAPTCHA bypass
Reddit is a major platform for community research, brand monitoring, sentiment analysis, and automated content distribution used extensively by marketing agencies. It deploys reCAPTCHA v3 invisibly during account creation and login, evaluating behavioral trust scores in the background rather than presenting a visible puzzle. Marketers and researchers bypass this using antidetect browsers assigned unique fingerprints, combined with residential proxies and human-like scrolling and dwell-time simulation. This approach maintains high trust scores, keeping accounts active across long-term campaigns.
Bypass Discord CAPTCHA
Discord is a leading community and communication platform where businesses manage brand servers, run automated bots, and create large volumes of accounts for outreach and community seeding. It uses hCaptcha during account registration and suspicious login events, which it verifies through HTTP-level behavioral analysis and IP reputation scoring. Teams bypass this using residential proxy rotation at the request level, combined with hCaptcha-solving APIs that intercept the challenge token and inject it directly into the registration HTTP flow. Pairing verified mobile IPs from pools like CyberYozh maximizes account creation success rates while minimizing ban risk.
Bypass CAPTCHA in specific browsers with CyberYozh
Before wrapping up, let’s summarize everything with a quick algorithm.
Setting up a CAPTCHA bypasser
Basically, to bypass CAPTCHA, one needs to select a proxy, develop a web strategy, automate the process, and, if CAPTCHA is still present, use an antidetect browser to create a separate web identity.
Set up a proxy with a desired geolocation. Check its trust crore before usage with the IP Checker service.
Determine a strategy that includes IP rotation timing, IP range, and optimal web activities that won’t look unnatural.
Create antidetect browser profiles for each activity and assign separate IPs for them, if needed.
Based on the strategy, build an automation script for web workflows, such as form filling, post writing, data scraping, and so on.
Make sure to follow the guidelines and recommendations described here, such as using separate fingerprint sets and setting realistic timing during automation, as website protection takes all of that into account and can block request patterns that appear unnatural.
Wrapping up
Websites deploy CAPTCHA to filter out bots, but this inevitably blocks legitimate business automation too. The most reliable bypass combines rotating residential or mobile proxies, antidetect browsers with unique fingerprint profiles, and human-behavior simulation scripts. Together, they make automated sessions indistinguishable from real users and keep critical business workflows uninterrupted.
Explore CyberYozh's proxy catalog now to find the best option for you, and keep your web operations secure and efficient!
FAQ about CAPTCHA and bypassing it
What is CAPTCHA and why do websites use it?
CAPTCHA is an automated security test distinguishing humans from bots. Websites use it to prevent spam, credential stuffing, DDoS attacks, and unauthorized scraping.
What are the main CAPTCHA types in 2026?
Major types include reCAPTCHA v2 checkbox, invisible v3 score-based, hCaptcha, Cloudflare Turnstile, and Arkose Labs FunCaptcha, each using different behavioral and visual verification methods.
What triggers a CAPTCHA challenge during automation?
Common triggers include datacenter IP usage, missing browsing history, fingerprint inconsistencies, rapid repetitive actions, and uniform interaction patterns with no mouse movement variance.
Which proxy type is best for bypassing CAPTCHA?
Mobile and residential proxies carry the highest trust scores. Datacenter proxies are fast but easily flagged by platforms like Cloudflare and Amazon.
How do antidetect browsers help bypass CAPTCHA?
They generate unique synthetic fingerprints — including Canvas hashes, User-Agent strings, and WebGL data — making each session appear as a distinct, genuine human user.
Can Selenium, Playwright, or Puppeteer bypass CAPTCHA automatically?
Yes, when configured with stealth plugins, randomized delays, curved mouse simulation, and rotating residential proxies, these tools reliably pass most modern CAPTCHA systems.
Is bypassing CAPTCHA legal for business purposes?
Legality depends on jurisdiction and platform Terms of Service. Scraping publicly available data is generally permitted, but bypassing access controls on private systems may violate applicable law.
How does reCAPTCHA v3 differ from v2?
Unlike v2's visible checkbox or image puzzle, v3 runs invisibly in the background, assigning a continuous risk score based on behavioral signals like typing cadence and scroll patterns.
What is the most effective full-stack CAPTCHA bypass setup?
Combining CyberYozh's residential or mobile proxies with an antidetect browser profile and a Playwright or Puppeteer stealth script delivers the highest bypass success rates for production workflows.