Bypass Cloudflare: Best Practices to Skip Cloudflare Check

Today, let’s explore whether there is a way to bypass Cloudflare protections, and how to ensure you aren’t breaking the law. While Cloudflare is a large technology company that provides web infrastructure services to protect websites, it may also restrict legitimate activities, such as public data scraping or managing multiple accounts. The reason is that these activities require sending multiple requests per second and are often automated to improve performance, so Cloudflare flags them as bot-like and potentially harmful. As we’ll see, rotating proxies, along with tools like antidetect browsers and cloud phones, can help bypass these restrictions.
What is Cloudflare: A global web protection infrastructure
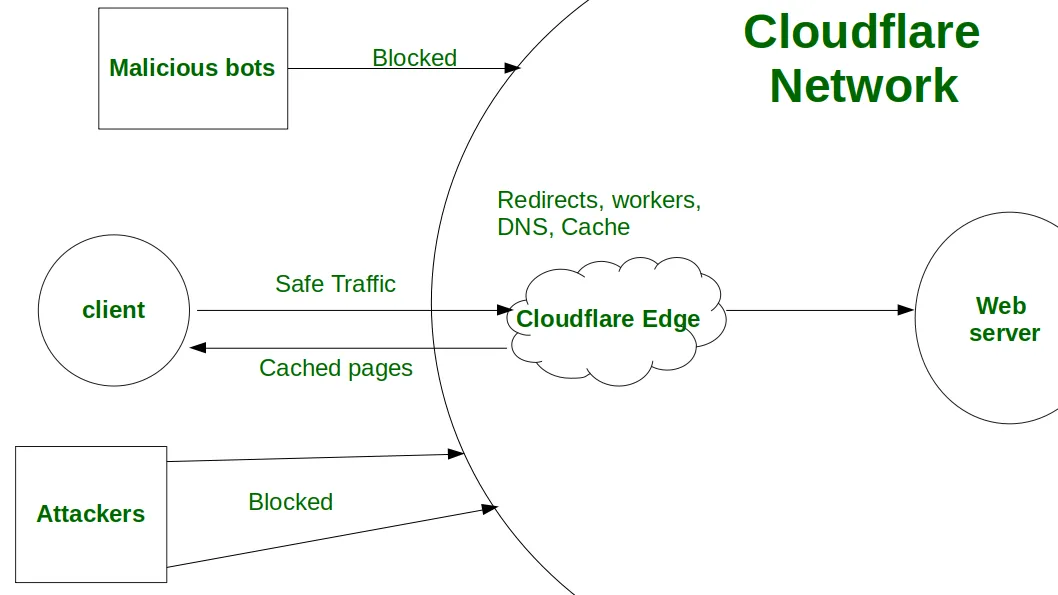
Cloudflare utilizes advanced anti-bot and anti-fraud systems, such as Web Application Firewall (WAF), Bot Management, and Turnstile, to protect websites from DDoS attacks, malicious scraping, account takeovers, and spam. These systems act as intermediaries between a client and a server, analyzing browser fingerprints, TLS/HTTP configurations, and user behavior to distinguish legitimate human traffic from automated scripts.
Read CyberYozh’s article about checkers and parsers to explore how platforms reveal and block suspicious activities
If a visitor's digital fingerprint appears suspicious, Cloudflare triggers JavaScript challenges or Turnstile CAPTCHA to verify human presence. It can also block IPs with a low trust score, disabling them from accessing the website. Activities like web scraping, account automation, and bulk ad placement, especially when they’re automated, appear unnatural and bot-like, so Cloudflare often restricts them even if they’re legitimate.
Check the IP trust score quickly with CyberYozh’s IP checker to ensure you won’t be blocked.
Cloudflare Web Application Firewall
Web Application Firewall (WAF) is a cloud-based security system that protects web applications and APIs by analyzing and filtering incoming HTTP/HTTPS traffic in real time. It’s an intermediary between the client and the application, evaluating every request against sets of rules (called rulesets) to block malicious activity, such as SQL injection, cross-site scripting (XSS), or DDoS attacks, while allowing legitimate traffic to pass through. WAF evaluates the request using several methods:
Signature-based detection: The WAF compares incoming traffic against a continuously updated database of known attack signatures, instantly blocking payloads that match recognized threats.
Custom rules: Administrators can write specific rules using a flexible expression syntax to filter traffic based on IP addresses, geolocations, URL paths, HTTP headers, or body content.
Machine learning: Cloudflare applies machine learning algorithms to detect anomalies and emerging threats that may not yet have a known signature.
Execution order: Requests are evaluated in a specific sequence, starting with IP Access rules, then Custom rules, and finally Rate-limiting rules. The first rule that triggers a terminating action (like Block or Managed Challenge) stops further processing.
Businesses can use specialized tools, such as antidetect browsers and proxy networks, to mimic human behavior and successfully bypass these protections.
To learn more, explore web scraping automation as a typical practice that requires proxies.
Cloudflare bot detection tools
Cloudflare employs a multi-layered approach to detect and mitigate malicious bot traffic while allowing legitimate human users and verified bots (like Googlebot) to access websites seamlessly. These detection mechanisms are part of Cloudflare's Bot Management and Super Bot Fight Mode products, which analyze billions of requests daily across its global network to continually update its threat intelligence.
Read more about web scraping best practices in CyberYozh’s article.
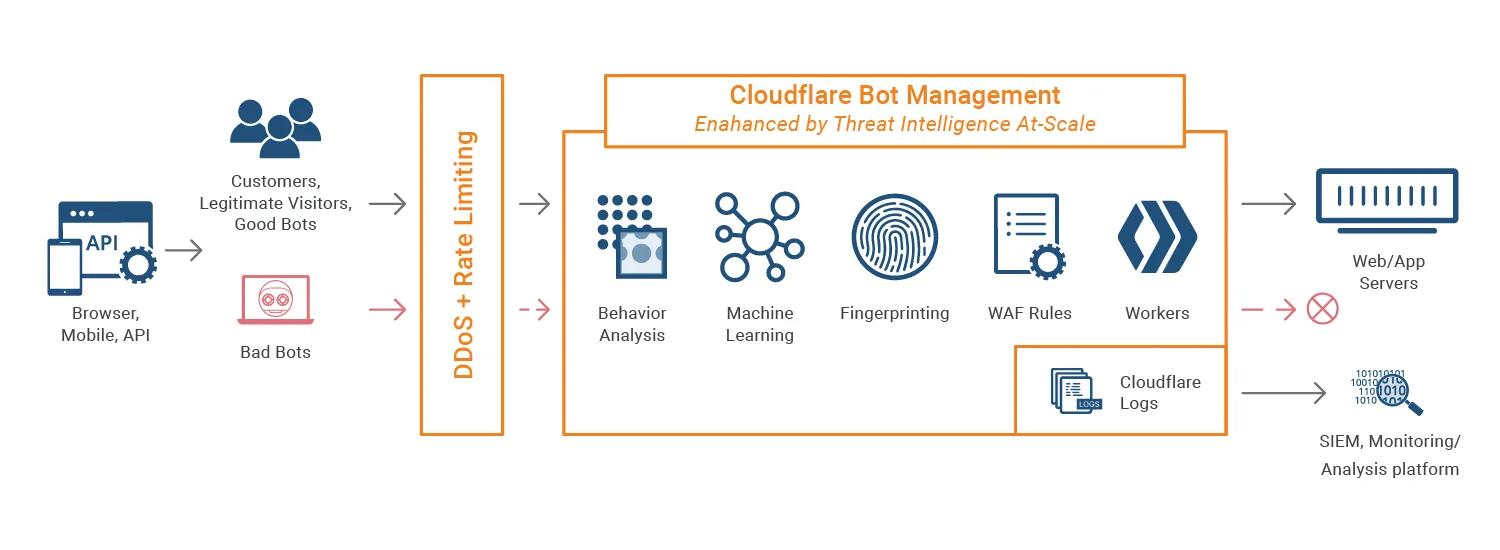
When a request hits a Cloudflare-protected site, it is evaluated in real time across several detection engines. Each request is ultimately assigned a Bot Score ranging from 1 (definitely automated) to 99 (likely human). Here is how it works:
Heuristics engine checks incoming requests for obvious signs of automation (e.g., Python code), bad IP reputations, and abnormal HTTP headers. If a request matches a heuristic rule, it is immediately flagged as a bot.
Protocol and network fingerprinting to ensure that the request is made from a real device via a legitimate browser. If a script tries to spoof a Chrome User-Agent but uses a TLS fingerprint that doesn't match a real Chrome browser, Cloudflare flags the mismatch.
Machine learning engine uses behavioral modeling trained on Cloudflare's massive global network traffic to spot anomalies. It evaluates session flow, request rates, and patterns that deviate from normal human browsing to assign the Bot Score.
Active challenges (Turnstile & JS): If a request's bot score is suspiciously low but not an outright block, Cloudflare issues a Managed Challenge or a Turnstile challenge to evaluate application-level behavior.
As a result, if the request has a low Bot Score and isn’t marked as a verified bot, it’s either outright blocked or challenged by CAPTCHA. Bulk, automated requests, typical for various business activities, may fall into this category.
Explore IP rotation to avoid blocks and understand how it may help with the Bot Score.
Is it legal to bypass Cloudflare?
Cloudflare is the service that protects websites from unauthorized access and requests that resemble DDoS attacks. So, is trying to bypass these protection layers actually legal? The answer depends on your reasons, and if you don’t violate websites’ Terms of Service and use bypass techniques for legitimate business purposes, it’s legal. For example, the following activities may require it:
Web Scraping: Extracting competitor pricing, product catalogs, and market trends from public websites to adjust corporate pricing strategies and maintain market competitiveness.
Social Network Management: Aggregating public sentiment, managing multiple brand accounts, and monitoring brand mentions across platforms using automated tools without triggering security blocks.
Customer Data Analysis: Gathering publicly available customer reviews and feedback from various retail platforms to analyze consumer sentiment and improve product development cycles.
Web Advertising: Verifying ad placements, checking for affiliate fraud, and ensuring localized campaigns display correctly across geographic regions using automated proxy networks.
SEO Monitoring: Tracking keyword rankings, monitoring competitor backlinks, and auditing search engine result pages (SERPs) across global locations to optimize digital marketing performance.
Travel Fare Aggregation: Scanning multiple airline and hotel websites simultaneously to provide consumers with real-time, consolidated price comparisons and immediate booking availability.
In many cases, bypassing Cloudflare is the only way to complete your work, as its protections block processes that make frequent web requests, including those your business needs.
How to bypass Cloudflare: Practical approaches
Taking that, let’s explore several ways to bypass Cloudflare protections.
Using proxy for Cloudflare checks
Proxy networks like CyberYozh, with its 50M+ residential and mobile IP addresses worldwide, help reduce the risk of triggering Cloudflare's bot detection by routing requests through IPs with high trust scores and genuine geolocation data. Routing traffic through residential or mobile proxies makes automated requests appear as legitimate user sessions. CyberYozh supports dynamic IP rotation across HTTP and SOCKS5 protocols, ensuring that scraping operations maintain consistently high Bot Scores throughout a session.
Read how proxies help with bypassing CAPTCHA to learn more.
Using antidetect browsers or cloud phones
Antidetect browsers and cloud phones offer the next level of protection by providing genuine, unique browser and device fingerprints that Cloudflare's ML engine treats as distinct human devices. Unlike standard headless browsers that leak automation flags, antidetect browsers make each session virtually indistinguishable from a real user. When paired with mobile or residential proxies from CyberYozh, each session presents a fully coherent identity that matches IP geolocation, device fingerprint, and browser behavior.
Learn more about antidetect browsers and cloud phones in CyberYozh’s dedicated articles.
Using a direct connection via IP
In many cases, if one knows the IP address of a target website, one can establish a direct connection with it, bypassing all intermediaries, including Cloudflare infrastructure. This method requires learning the target website’s IP address and may be tried before using proxies or antidetect tools, though it doesn’t always work.
Using CAPTCHA-solving automation
Bypassing Cloudflare CAPTCHA using automated CAPTCHA solvers is the final option, which basically relies on brute force, unlike all other methods that focus on bypassing and preventing Cloudflare challenges rather than solving them. Read more about CAPTCHA solvers to understand when this method is applicable, but it’s better to use it as a backup option if Cloudflare’s CAPTCHA is still triggered.
How to find a website’s IP address
There are several ways to find the target website’s IP address. Let’s explore them.
Historical DNS records for the domain, which can be accessed via services like SecurityTrails and ViewDNS, and contain the website’s IP address, among other data
Email headers, which may contain the sender’s IP if it doesn’t use services like Google Workspace, can be accessed by viewing the email source and searching for keywords Received: and Originating-IP:
SSL/TLS certificates can be searched using tools like Censys, and then the website’s IP can be found in these certificates
Search via Shodan, a tool that searches the Internet-connected devices, can be used to reveal the website server’s IP via its unique page content
These methods aren’t universal, and in many cases, they won’t work because the target IP may be absent from databases, certificates, and other sources. Still, they can be tried if revealing a website’s IP is needed.
Final thoughts: Why is bypassing Cloudflare needed sometimes
If you can’t pass Cloudflare verification, you need a service that can help you bypass it. While Cloudflare's infrastructure protects the web from malicious agents, it also prevents many legitimate agents from doing web scraping, multiaccounting, data analysis, travel fare aggregation, and other activities that rely on frequent, bulk requests. That’s why proxy networks and antidetect browsers need to be used there, rotating requests among clean IP addresses and presenting genuine device fingerprints. While other methods may be used, the proxy infrastructure is the most reliable, allowing businesses to automate their operations without exposing their data or triggering Cloudflare bans. So, check our proxy catalog now and select those that suit your needs.