Are Proxies Safe? Real Risks, Data Security & How to Avoid Leaks (2026 Guide)

You buy a proxy to protect your activity. But here's what most people miss: the proxy itself sees everything. And if you picked the wrong one, you just handed your logins, cookies, and private messages to a stranger.
A 2018 study of free proxy services revealed that 92% of open proxies are unresponsive to requests and unreliable. Some of them have injected ads and varying logging policies. Meanwhile, platforms like Instagram and TikTok have gotten better at detecting datacenter IPs, pushing users toward residential and mobile proxies, which are more expensive and harder to vet.
If you’re running multiple accounts, automation, ads, or scraping, your proxy isn’t just a connection tool. It’s part of your security system. And in many setups, it’s the weakest part because most proxy setups are fundamentally unsafe.
This guide breaks it down:
When proxy setups remain safe under scraping, multi-accounting, and automation workloads
How proxies can expose your data through traffic handling, logging, or weak IP reputation
What configuration mistakes lead to leaks, bans, and account linking
A step-by-step secure proxy setup for stable, low-detection operations.
TL;DR
Free and low-quality proxies are risky because IPs are often shared, reused, and have unknown abuse history.
Most bans, leaks, and account linking come from bad IP reputation and unstable routing, not from using proxies themselves.
Safe setups require clean IPs, consistent sessions, and control over how traffic is routed.
Are proxies safe?
Proxies can be safe, but only under the right conditions. The main risk is not the proxy itself, but how it is sourced and managed, especially in terms of IP reputation, sharing, and traffic control.
In practice, there are two setups:
Safe setup:
Clean IPs with known reputation
Stable sessions per account
Controlled routing and isolation
No shared abuse history
Unsafe setup:
Free or recycled proxy pools
Shared IPs across unknown users
Unstable or random rotation
No visibility into IP history or usage
Most real-world failures (bans, CAPTCHA loops, account linking, or data exposure don’t come from using proxies. They come from running traffic through the unsafe side of this split.
How proxies protect your data
A proxy sits between you and the target platform, acting as an intermediary for all outgoing and incoming requests.
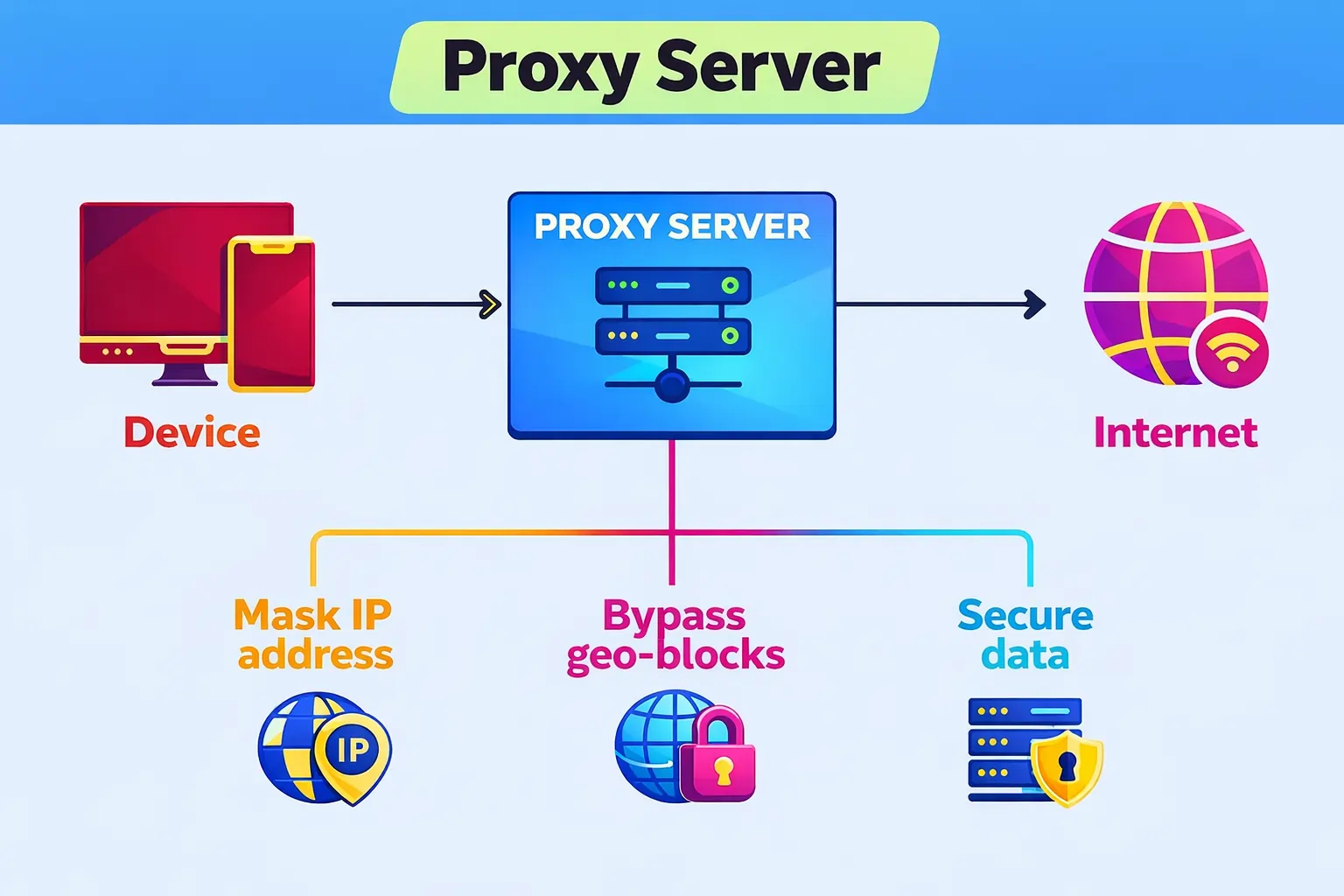
Instead of a direct connection:
You → Website
Traffic is routed through a proxy layer:
You → Proxy → Website
In practice, this structure changes how your data is handled at the network level. When configured correctly, it provides three core functions:
IP masking: the target platform sees the proxy IP, not your real IP
Environment separation: different accounts, sessions, or workflows can be isolated through separate proxy connections
Traffic control layer: requests are routed through a defined intermediary layer instead of direct access.
However, this architecture also introduces a critical dependency: the proxy becomes part of your trust boundary.
Every request passes through it, meaning the provider handling that proxy has a potential position in your data flow. If the proxy infrastructure is unstable, misconfigured, or untrusted, it becomes a point where traffic can be exposed, logged, or correlated across sessions.
When proxies become a security risk
In real proxy-based workflows, security issues come from infrastructure quality, IP history, and how traffic is handled across scaling systems like scraping, automation, and multi-account setups.
1. Free or low-quality proxies
Free and low-quality proxies usually operate without strict control over traffic handling. Requests may pass through shared or untrusted nodes where logging, modification, or reuse of data is possible. IPs are often recycled across multiple users and exposed to public abuse patterns.
This creates unstable sessions, rapid IP blacklisting, and increased detection rates in automation and account-based workflows. In practice, the proxy layer stops behaving like a security boundary and becomes part of the exposure surface.
2. Shared & abused IPs
Shared proxy pools mean multiple users operate on the same IP history. That history does not reset. If an IP was previously used for spam, automation, or policy violations, that reputation is inherited by every new session routed through it.
As a result, platforms reduce trust at the network level, which leads to:
Increased CAPTCHA challenges
Account limitations
Degraded performance even when user behavior is correct.
Check your IP before your automation breaks or accounts get flagged using CyberYozh's free tool. It checks the IP reputation across 50 databases and returns you an instant report.
3. No isolation between accounts
A common structural issue is running multiple accounts without proper separation of identity layers. When accounts share IPs, browser fingerprints, or inconsistent routing setups, platforms can link them at infrastructure level.
This leads to account linking, pattern detection, and cascading bans where one flagged account increases risk for the entire group. The risks are even higher on sensitive platforms like Instagram, Facebook, or TikTok accounts.
4. Unencrypted or misconfigured proxies
Misconfiguration removes the protection layer entirely. DNS leaks, routing errors, or missing encryption can expose the real IP address or bypass the proxy path completely.
In these cases, the proxy is no longer part of the request flow, and anonymity is effectively broken at the network level.
5. Untrusted providers
Untrusted proxy providers introduce security risks. If the infrastructure uses unstable routing, unclear logging, or overloaded IP pools, traffic becomes unpredictable and harder to control.
In structured setups, teams typically rely on managed proxy infrastructures like CyberYozh for stable routing and controlled IP pools. This improves consistency in scaling workflows and increases the percentage of successful operations.
Proxy as a vulnerability: How your data is stolen
You are right to be wondering “Can proxies steal data?” A proxy is not just a routing tool; it is a traffic processing layer that decrypts, handles, and forwards requests between the user and the target platform. If that layer is untrusted, it becomes part of the data exposure.
1. Man-in-the-middle (MitM) attack
The main risk in proxy traffic is Man-in-the-Middle processing. A proxy encrypts traffic between the user and itself, but must decrypt it before forwarding requests.
At that point, it can access unencrypted data inside the flow.
This may include logins, passwords, session cookies, payment data, and private messages. Free and low-quality proxies are especially risky because their infrastructure often relies on traffic collection or resale rather than secure routing.
2. Data logging policy
Data logging policy defines what user and connection data a proxy provider records. Proxy security risks depend on what is logged and how it is used. Operational logging is standard and includes connection time, bandwidth usage, and authentication events. It is required for stability, billing, and abuse control.
Activity logging is different. It tracks user behavior such as visited websites and request-level data. In low-trust environments, this data can be stored, analyzed, or monetized.
3. Malware and traffic injection
Because proxies control request flow, they can modify traffic before it reaches the user. When HTTPS traffic is decrypted for forwarding, content can be altered or injected before re-encryption.
This enables ad injection, content modification, phishing redirects, credential interception, session hijacking, and replacement of downloaded files with malicious payloads.
4. The “bad neighbor” effect (shared proxies)
Shared proxies reuse the same IP across multiple users. If that IP was previously used for spam, automation, or abuse, its reputation carries over.
This leads to reduced trust, increased CAPTCHA frequency, access restrictions, and faster detection in automated workflows.
5. DNS leaks
DNS leaks occur when domain resolution bypasses the proxy and is handled by the ISP. Even with an active proxy, DNS requests can expose visited domains externally, revealing browsing patterns at the network level.
6. WebRTC leaks
WebRTC is a browser-level system that can expose real IP addresses outside proxy routing. In some cases, it bypasses proxy configuration entirely, creating a direct identity leak path at the browser layer that must be controlled separately.
Proxy types & security differences
Not all proxies behave the same. Their security level, detection resistance, and stability depend on the source of the IP and how the underlying infrastructure is built. In real-world workflows like scraping, automation, and multi-account management, proxy type directly defines trust signals and failure risk.
Mobile proxies
Mobile proxies use real 4G/5G IPs from mobile carriers. It makes them the highest-trust category due to mobile network behavior that platforms treat as legitimate user traffic. Thus, they are the least likely to trigger detection.
Best for: social media operations, account farming, and high-sensitivity workflows where account survival and trust signals matter more than speed.
Residential proxies
Residential proxies route traffic through real ISP-assigned user devices, which gives them legitimacy and stable session behavior. They are stable and scalable than mobile proxies in structured workflows, but slightly more detectable under aggressive platform analysis.
Commonly used for: scraping, browsing automation, and multi-account setups where balance between stability, cost, and trust is required.
Datacenter proxies
Datacenter proxies are generated from server infrastructure, such as AWS. It makes them fast and scalable but lower in trust from the perspective of most platforms. Because their IP ranges are known, they are more likely to be rate-limited, flagged, or blocked under strict detection systems.
Best for: non-sensitive or high-volume tasks where speed and cost efficiency matter more than stealth or account safety.
Why CyberYozh (infrastructure built for stable operations, not just IP access)
Most proxy services stop at giving you an IP. But in real workflows (scraping, automation, ads, or multi-accounting) proxy becomes part of your infrastructure. And that’s where safety starts to depend on unstable IP pools, unknown reputation history, and missing risk controls.
Here’s why CyberYozh is built different:
Managed IP pools instead of random recycled proxy sources – reduces the chance that an IP was previously abused for spam or platform violations.
IP reputation and fraud-risk checks before use – verify whether an IP is clean or already flagged before routing real traffic through it, minimizing bans and CAPTCHAs.
Stable session handling and controlled routing – reduces random IP switching, session breakage, and mixed-user IP exposure, which are common causes of account linking and detection.
Key features:
50+ million IPs across 100+ countries
Stable distribution of mobile, residential, and datacenter IPs designed for long-term use, not recycled public pools.Unlimited mobile LTE/5G proxies with real carrier networks
Built for high-trust environments like social media platforms, ads, and account-based systems where session stability matters.Residential + datacenter coverage in one ecosystem
Instead of switching providers, you match the proxy type to the task: scraping, automation, or high-speed execution.API-first automation support
Works directly with Scrapy, Selenium, Playwright, Puppeteer, Postman, and custom scripts, so proxies fully integrate into workflows.SMS activation + verification tools in the same system
Account creation, scaling, and verification are handled in one environment instead of separate vendors.
Use case: A social media agency in Barcelona manages 90 Instagram and TikTok accounts for e-commerce brands using CyberYozh mobile and residential ISP proxies. Each account runs on a dedicated IP. Over 14 months, they scaled from 25 to 90 accounts with zero bans, no detected data leaks, and stable automation without CAPTCHAs, maintaining predictable performance without added operational overhead.
What a safe proxy setup looks like
A safe proxy setup is about structure and control, not just having an IP. Here’s what it should look like in practice:
One account = one stable identity
Each account runs on a dedicated IP or a consistent sticky session, without random switching between different IPs.Consistent session behavior
The same account should not constantly change location, IP type, or network pattern, as this triggers verification and trust loss.Clean IP reputation
IPs are checked before use to avoid previously abused, blacklisted, or flagged addresses that increase ban risk.Controlled IP rotation (not random)
Rotation only happens in a structured way, not continuously or unpredictably during active sessions.Stable routing under load
The setup should work the same way whether you run 5 accounts or 100 — without sudden blocks, resets, or performance drops.Pre-check before execution
IP quality and risk signals are verified before traffic starts, instead of reacting after issues appear.
In short: a safe proxy setup is predictable, isolated, and based on clean IP history — not shared infrastructure or uncontrolled rotation.
How to Choose a Secure Proxy
Choosing a secure proxy is not about speed or marketing labels — it’s about whether you can trust the provider’s infrastructure, policies, and IP quality in real use.
Check reputation and business model. Avoid free proxies for anything sensitive. Reliable providers are paid services with a proven track record and transparent operations. If there is no clear business model, you are usually the product, not the client.
Review the privacy policy, not the slogans. Look for what is actually collected and why. A trustworthy provider clearly defines what data is stored (billing, account info) and does not track or sell browsing activity or traffic content.
Check jurisdiction and legal transparency. The country where the provider operates matters. Strong privacy jurisdictions and transparent company registration reduce hidden legal and compliance risks.
Use modern secure protocols. Prefer providers that support HTTPS and SOCKS5 with proper authentication. Weak or outdated protocol handling increases exposure during traffic transmission.
Prefer dedicated over shared proxies. Dedicated (private) proxies eliminate “bad neighbor” effects and prevent reputation contamination, which is one of the most common causes of bans and CAPTCHAs.
Conclusion
Proxies are safe only when the infrastructure is controlled. The proxy itself is not the risk; shared IP history, unstable routing, and lack of visibility over traffic handling are what create bans, leaks, and account linking.
CyberYozh combines managed IP pools, reputation checks, and stable session control, so proxy usage is not based on guesswork but on verified infrastructure conditions.
→ Explore catalog of reliable proxies starting from $0.9/GB.