
What is Proxy Service: 2026 Guide to Proxy Types and Use Cases
A proxy service is a web infrastructure provider that provides access to multiple proxy servers, so users can route their internet traffic through intermediary IP addresses. There are various proxy use cases, which include privacy enhancement, account management, access control, web scraping, SEO purposes, and more. Let’s explore
What is meant by proxy service: Basic definition and purpose
A proxy is an intermediary between your device and the Internet. It ensures that your original IP isn’t exposed and no restrictions can be applied to it. Additionally, as we’ll see, a proxy functionality may be greatly expanded by manual customization of a dedicated proxy server, ensuring that it processes the requests in a way the proxy owner needs.
Want to know more? Explore the CyberYozh knowledge base and learn everything you need about setting up and customizing a proxy for personal and business tasks.
How does a proxy service work
Let’s explore the core request-response flow that is the basis of how these services work.
Client request initiation starts when a client sends a request to the proxy server instead of directly to the destination, using a proxy configuration.
Request validation is processed by the proxy server, which checks the request to review access policies, consulting authentication services and control lists.
Connection establishment proceeds if the authorization is accepted and no valid cache exists, as the proxy opens a new connection to the destination server.
Response processing occurs after the destination server responds, as the proxy can inspect, modify, or filter the response content
As one can see, a proxy server can be customized to authorize one type of request and decline another, ensuring that no unauthorized request can access the client and reveal their IP and other settings, while every request can be processed separately. Usually, proxy services offer various types of servers for different purposes, serving customers from web scraping specialists to SMMs and journalists.
Difference between proxy and VPN
Virtual Private Networks (VPNs) and the related Virtual Private Server (VPS) service are similar instruments, as they also offer traffic protection and various customization tools. However, they are used differently: usually, a VPN service offers a separate protected virtual server with a dedicated IP, while a proxy can be customized so that every request is processed from a different IP in a proxy pool.
Here are specific implications:
Encryption: VPN encrypts all incoming traffic based on VPS settings, while proxies can be customized in terms of which data they process and how.
Coverage: VPN redirects all client traffic via the virtual network, while a proxy can route traffic from specific apps using specific IP ranges and configurations
Speed: Due to higher customization, proxies are generally faster than VPNs, which process all incoming traffic in the same way
Usage: Proxies are used for business tasks requiring high customization, while VPNs are good for general network protection
What is a proxy service used for
There are various use cases of proxy servers, and we’ll explore them after diving deeper into proxy peculiarities. Now, let’s review which specific activities can be performed using a proxy service.
IP masking replaces the client's real IP address with the proxy's IP, hiding the client's identity and data from destination servers
IP rotation automatically switches between different IP addresses from a proxy pool for each request or session to distribute traffic load and avoid detection
Geolocation management presents IP addresses from specific geographic regions to access location-restricted content or simulate user presence in different locations
Usage monitoring tools track and analyze internet usage patterns, bandwidth consumption, and user activity across the network and send data to the client
Rate limiting controls the number of requests from specific sources within defined time windows to prevent abuse or overload
Content filtering inspects and blocks specific content types, sources, or patterns based on predefined rules and policies
Protocol translation converts between different protocols (HTTP/HTTPS, SOCKS, FTP, etc.) to enable cross-protocol communication
Strong authentication enforces multi-factor authentication methods to prevent unauthorized proxy server access for additional protection
Do you need to ensure that the IP address of your interest isn’t affiliated with fraud or scam? Use our free IP Checker!
Types of proxy services
Based on the IP type and protocol technology, there are several types of proxy services. As we’ve explored the proxy basics, now it’s time to explore these types.
Mobile proxy service (LTE/5G)
Mobile proxies route internet traffic through IP addresses assigned by mobile carriers via cellular networks. Nowadays, only 4G (LTE) and 5G networks are widely used; others are considered very slow and deprecated. These proxies are characterized by the following features:
Use physical SIM cards or virtual SIM technology connected to mobile operator infrastructure.
Share the same IP address among thousands of real users, so individual users are nearly impossible to isolate.
IP addresses change automatically during normal mobile network operations, such as reconnections.
Trust score is highest among all proxy types, as the traffic appears identical to legitimate mobile user activity.
Mobile proxy providers deploy physical hardware with SIM cards or use virtualization to create proxy instances with carrier-assigned IPs. They’re highly recommended for those seeking to interact with social media actively or manage multiple accounts, as it’s nearly impossible to block an IP from the mobile range.
Residential proxy service (static/rotating)
Residential proxies use IP addresses assigned to home users by local Internet Service Providers (ISPs). These IPs belong to real household internet connections rather than commercial hosting facilities. There are two types of them, and it’s important to select the one according to the specific activity:
Static proxy maintains the same IP address for extended periods (days, weeks, or months). The IP remains constant across all requests, creating a consistent session identity similar to a regular home internet user. It’s ideal for building a long-term identity for a brand or business.
Rotating proxy automatically switches IP addresses at defined intervals or per request. The rotation mechanism pulls from large IP pools (often millions of addresses) distributed across geographic regions. It should be used when managing multiple accounts or participating in different activities.
Residential IP pools usually include millions of residential IPs across multiple countries and cities. They offer medium-to-high legitimacy, as they simulate real ISP users, but they still may be banned if participating in spam-like activities on social media, for example, sending multiple similar requests from a single IP. To prevent this, it’s essential to choose a static or rotating proxy wisely.
Explore in-depth the rotation error and 6 other critical proxy usage mistakes in CyberYozh's dedicated guide.
Datacenter proxy service
Datacenter proxies use IP addresses hosted in commercial data centers operated by cloud providers, such as AWS, or specialized proxy hosting companies. For users who prefer speed and scalability over privacy and ban risks, they offer:
Highest throughput and lowest latency among all proxy types due to enterprise-grade network infrastructure.
High scalability with the ability to deploy thousands of proxies instantly, as they're essentially dedicated virtual machines.
Consistent performance and stability without the variability of residential or mobile networks.
Most affordable option per proxy, often 10-50x cheaper than residential or mobile proxies.
However, these IPs are not connected with residential ISPs or mobile carriers, and they’re usually already flagged as not associated with real users. It makes their usage highly inefficient when interacting with social media or other bot-protected websites, as they usually automatically block datacenter IP ranges or challenge them with CAPTCHA. They’re good for scraping large open databases, specifically dedicated to such activities.
Proxy types: Comparison table
To quickly compare three primary types of proxy IPs, here is a comparison table, so you can decide quickly which type suits you best.
Property | Mobile (LTE/5G) | Residential | Datacenter |
IP Origin | Mobile carrier networks | Home web providers | Cloud hosting providers |
Trust Score | Highest (real mobile users) | High (real homes) | Lowest (commercial servers) |
Detection Risk | Very low | Low to medium | High |
Speed | Moderate (cellular networks) | High (home networks) | Highest (enterprise networks) |
Cost | Highest ($50+/IP/month) | Medium ($5-30/IP/month) | Lowest ($0.50-5/IP/month) |
Scalability | Limited (SIM-card dependent) | High (home IP ranges) | Very high (large cloud servers) |
Best for | Social media interactions | General web activities | Open database scraping |
What are SOCKS5, HTTPS, and other protocols
Now, it’s time to dive deeper and explore the underlying technology of various proxy types, regardless of whether residential, datacenter, or mobile. A protocol type determines which types of data the IP service can process, so it’s essential to configure the server according to the data you’ll work with, which may include:
Web traffic (request-response pattern)
Game traffic (real-time communication)
VoIP traffic (audio/video streaming)
P2P traffic (file exchange via multiple connections)
IoT traffic (Internet of Things; control and sensor commands)
HTTP/HTTPS protocol is the most widely known one, as it works with the Web traffic, but SOCKS5 (Socket Secure version 5) is much more universal, and while it’s harder to set up, it’s highly preferred if you must work with data other than ordinary Web/API requests.
Read more about SOCKS5 and HTTPS protocols and their comparison in CyberYozh’s guide.
To be short, here are quick definitions:
HTTPS protocol uses ordinary HTTP requests for data processing, making it ideal for interacting with the Web, but unsuitable for other data types.
SOCKS5 protocol is a session-layer protocol that forwards all traffic types between a client and a proxy without protocol-specific interpretation.
Therefore, SOCKS5 is preferred if you need to work with file exchange systems, video/audio streaming, MMO games, and other platforms that process data differently from ordinary websites.
What is the best proxy service
Now, let’s review various proxy services in different categories and explore which one should be used in which case.
Universal proxy services: CyberYozh
CyberYozh is an example of a universal proxy service with advanced security features, robust integrations with other services for business process automation and optimization. It prioritizes accessibility, universality, and integration flexibility.
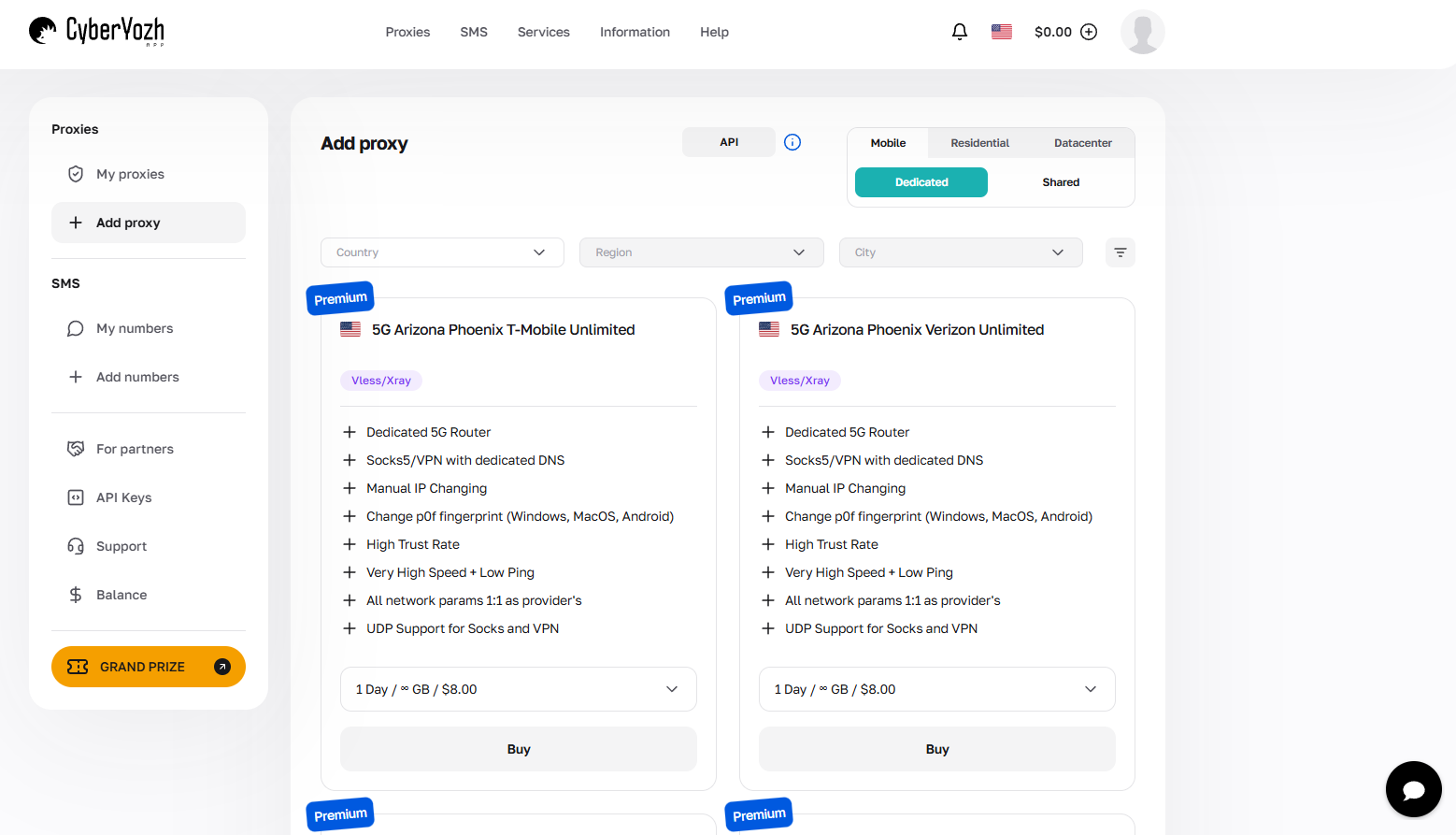
Its specific features include:
Advanced security features, including the Fraud Score system and highly configurable dedicated proxy servers with 99.99 success rate.
Integrated business services, such as SMS activation with virtual and residential numbers for accounts across popular platforms
Robust integration ecosystem with comprehensive APIs and built-in support for frameworks like Selenium, Puppeteer, and Postman
CyberYozh pricing starts at just about $1 per IP for the datacenter proxies, offering high accessibility without compromising quality, making it a universal solution for different teams.
Alternative solution: Bright Data
For large enterprises, solutions that offer very large IP ranges and complex data scraping tools may work better. They’re much more expensive and harder to use, but allow efficient scraping of very large data volumes. Bright Data is an example of such a service, which positions itself as the premium enterprise solution for large-scale web scraping operations and data intelligence.
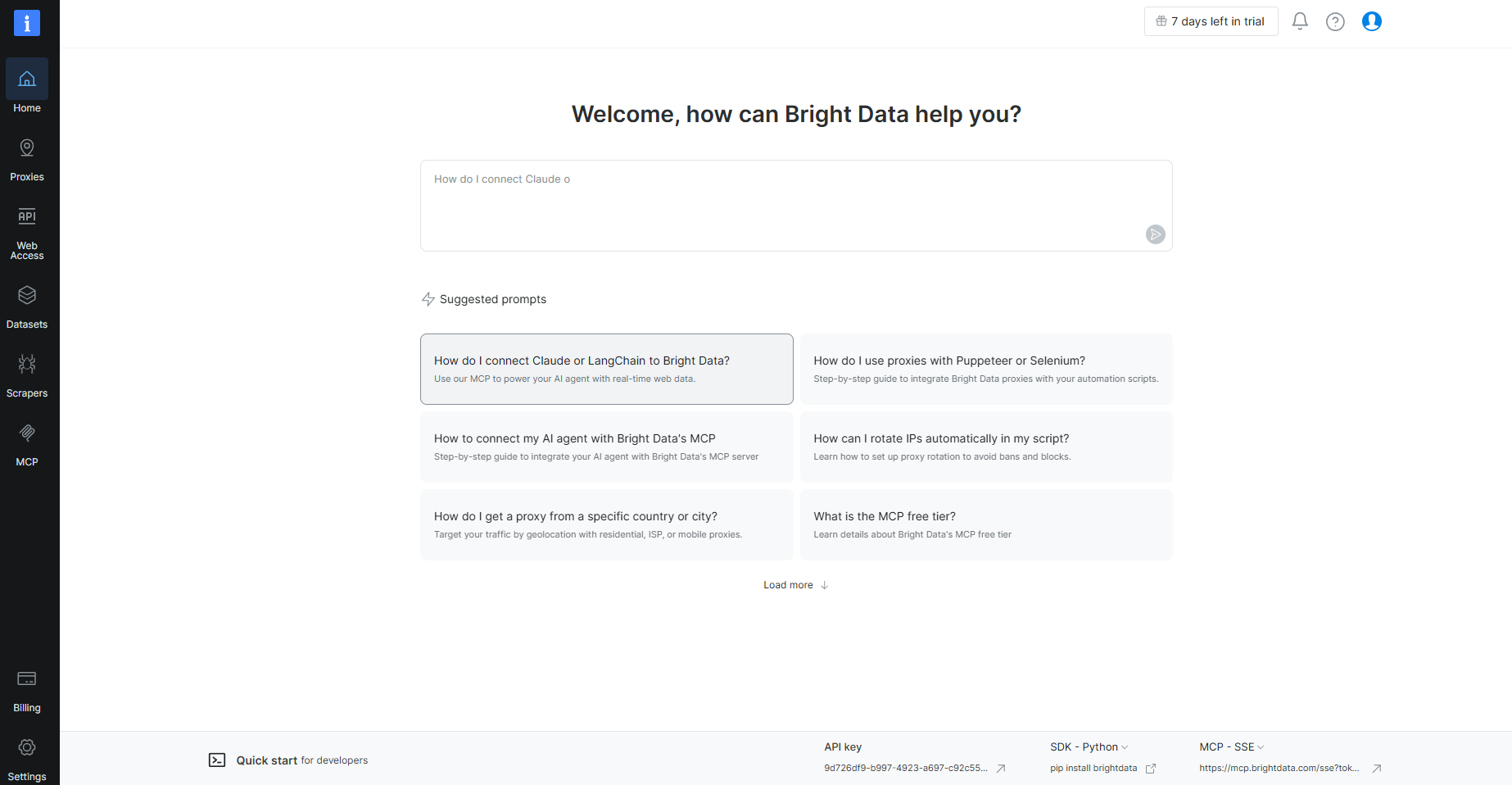
It’s characterized by:
Massive IP infrastructure across countries, cities, ZIP codes, and specific coordinates.
Advanced scraping ecosystem with Web Scraper APIs and specific programmable tools.
Enterprise pricing, tailored to each client's specific requirements rather than fixed packages.
Bright Data serves large data companies around the world, but its complexity and cost make it less suitable for small teams or individual users.
Comparing various providers
Here is a quick comparison table showing CyberYozh, Bright Data, and several other proxy providers, comparing their key characteristics and exposing their distinct features.
Provider | Pricing | Key Features | Best For |
CyberYozh | Low Datacenter: from $0.90/IP Mobile: from $4.99/day | - Fraud Score verification across 8+ systems - Integrated SMS activation services - Browser extensions & API access - Low fraud score IPs | Universal service for various business needs |
Bright Data | High Custom enterprise pricing (7-day trial available) | - Pre-built Web Scraper APIs - Ready-to-use datasets - Custom compliance solutions | Enterprise web scraping at a massive scale |
Oxylabs | High Datacenter: from $1.20/IP Mobile: $9/GB | - 99% uptime guarantee - Advanced targeting (ZIP, ASN) - Free 5 datacenter IPs | Enterprise data collection and intelligence |
Decodo | Medium Datacenter: from $0.60/GB Mobile: $8/GB | - Web Unblocker tool - Scraping API suite - 14-day money-back guarantee - City-level targeting | Mid-sized teams needing scraping tools |
SOAX | Medium Unified: from $3.60/GB (25GB = $90/month) | - All proxy types in one plan - UDP & QUIC protocol support - Customizable IP refresh rate - 195+ countries available | Growing businesses seeking flexible plans |
IPRoyal | Medium Datacenter: from $1.57/IP Mobile: $10.11/day unlimited | - Non-expiring traffic credits - Ethical IP sourcing - Unlimited mobile traffic option - Budget-friendly bulk discounts | Budget-conscious teams and small projects |
Smartproxy | Medium Datacenter: from $0.60/GB Mobile: $7.50/GB | - No-code scraping solutions - City & state targeting - User-friendly dashboard | Small teams prioritizing quick solutions |
Want more information? Compare CyberYozh with Oxylabs, Decodo, and SOAX in detail!
How to use proxy services
Setting up a proxy connection is easy. The only thing you need is a proxy infrastructure: a server with an IP range and dedicated configurations to process the required traffic types and protect your data.
Setup and technical usage
Here is a quick algorithm of how to set up and use the proxy.
Getting proxy infrastructure: Create an account with a proxy service and purchase a subscription or deploy a personal proxy server
Configuring the server: Set up the IP range, protocol (HTTPS/SOCKS5), and get your proxy credentials (IP, port number, username, password)
Connection authorization: Authorize via the WiFi settings, a browser extension, or a mobile apps, depending on your platform and protocol type.
Connection maintenance: Depending on your purposes, monitor traffic usage, manage rotation, and track other essential parameters we’ve discussed there.
Read more about setting up the proxy on Android and iOS.
Integration and APIs
Regardless of the proxy IP and its underlying protocol, it can be further customized to meet a specific client’s needs. It includes proxy server unique configurations and API integration with tools like Fiddler, Postman, or Crawl4AI. Let’s explore some of these features.
API usage for bulk operations, monitoring, traffic load balancing, and automated proxy management
Postman proxy configuration to route API requests through debugging proxies for inspection and automation
Crawl4AI integration for automated web scraping with rotating IPs and session management to prevent CAPTCHA and bans
Fiddler proxy chaining to intercept traffic and route through external proxy services for traffic inspection
Custom scripting using Python for automated data scraping and IP rotation
With these options, proxy infrastructure can solve a wide variety of business tasks. Let’s look closer at that.
Why to use a proxy: Use cases
Based on CyberYozh's experience, here are several distinct use cases, showing how proxy services streamline and secure business operations
Data scraping means collecting large-scale datasets, such as product catalogs, pricing information, and user reviews, for business intelligence, machine learning, and analytics. Proxies distribute requests across multiple IPs to bypass rate limits, avoid anti-bot detection systems, and maintain high success rates during large-scale data collection operations.
Social media management (SMM) implies managing multiple accounts across platforms without triggering security algorithms or spam/bot flags. Mobile proxies with unique IPs enable businesses to run numerous accounts for different clients, start influencer marketing campaigns, schedule content, and automate engagement activities without risks.
SEO optimization includes tracking search engine rankings accurately across different regions and devices without personalized results interfering with data. Proxies enable running thousands of search queries for keyword position tracking, competitor analysis, and local SEO monitoring without triggering rate limits or CAPTCHA.
Market analytics requires accessing region-specific market data, pricing information, and localized content from different geographic locations. Proxies enable businesses to emulate real users from the EU, US, Asia, Africa, and Latin America to gather accurate competitive intelligence, monitor local demand patterns, and analyze regional offers.
Lead generation implies activities like contact collection, profile extraction, business directory scraping, and audience segmentation. Private IPs allow automated tools to run reliably and discreetly while collecting publicly available business data, company information, and contact details.
Security assessments include threat analysis, penetration testing with permission, and infrastructure monitoring while maintaining anonymity. Proxies enable security professionals to verify brand protection compliance, collect reviews about products and services from localized websites, and conduct threat intelligence gathering without exposing their real IP addresses.
With responsible and ethical proxy usage, ban chances are minimal, while business efficiency grows greatly.
Wrapping up: The best proxy for you
Proxy services have evolved from simple IP masking tools into comprehensive infrastructure solutions that power modern digital operations. For managing social media accounts, conducting market research, or executing large-scale data collection, the right proxy configuration directly impacts operational success and security. By understanding proxy technical configurations and applications, businesses can leverage these services to maintain competitive advantages in increasingly complex digital environments.
Explore IP types (mobile, residential, datacenter), protocols (SOCKS5, HTTPS), and customization features that empower your business operations. Sign up to CyberYozh, select the plan that suits you best, and secure your digital presence now!
FAQs: What is proxy service
What is meant by proxy service in simple terms?
A proxy service provides intermediary servers that route your internet traffic through different IP addresses, hiding your real location and identity from destination websites. It acts as a middleman between your device and the internet, processing requests on your behalf.
What is a proxy service for Spotify?
Mobile or residential proxies bypass Spotify's geo-restrictions by routing your connection through IP addresses in the target country where specific content is available. This allows access to region-locked playlists, albums, and features without physically being in that location.
What is a SOCKS5 proxy service?
SOCKS5 is a session-layer protocol supporting both TCP and UDP traffic, making it ideal for gaming, VoIP, torrenting, and web scraping that requires protocol flexibility. Unlike HTTP proxies, it handles any traffic type without protocol-specific interpretation.
What is an anonymous proxy service?
An anonymous proxy hides your real IP address without revealing to target websites that you're using a proxy. Elite proxies like mobile LTE/5G offer the highest anonymity by using real carrier IPs shared by thousands of legitimate users.
What is a VPN and a proxy service difference?
VPNs encrypt all device traffic system-wide, providing comprehensive security but slower speeds. Proxies route specific application requests without encryption, offering faster performance for targeted tasks like web scraping and SEO monitoring.
What is Microsoft's streaming service proxy?
A network proxy within Microsoft 365/Teams environments that routes streaming traffic through corporate firewalls and infrastructure. It optimizes bandwidth allocation and ensures video conferencing compliance with enterprise security policies.
What is a web service proxy in API development?
A reverse proxy or API gateway positioned between clients and backend services, managing load balancing, authentication, rate limiting, and request routing. It provides a unified entry point for microservices architectures and protects backend infrastructure.
Helpful?
Share article
