What are Reverse Rotating Proxies and Who Needs Them

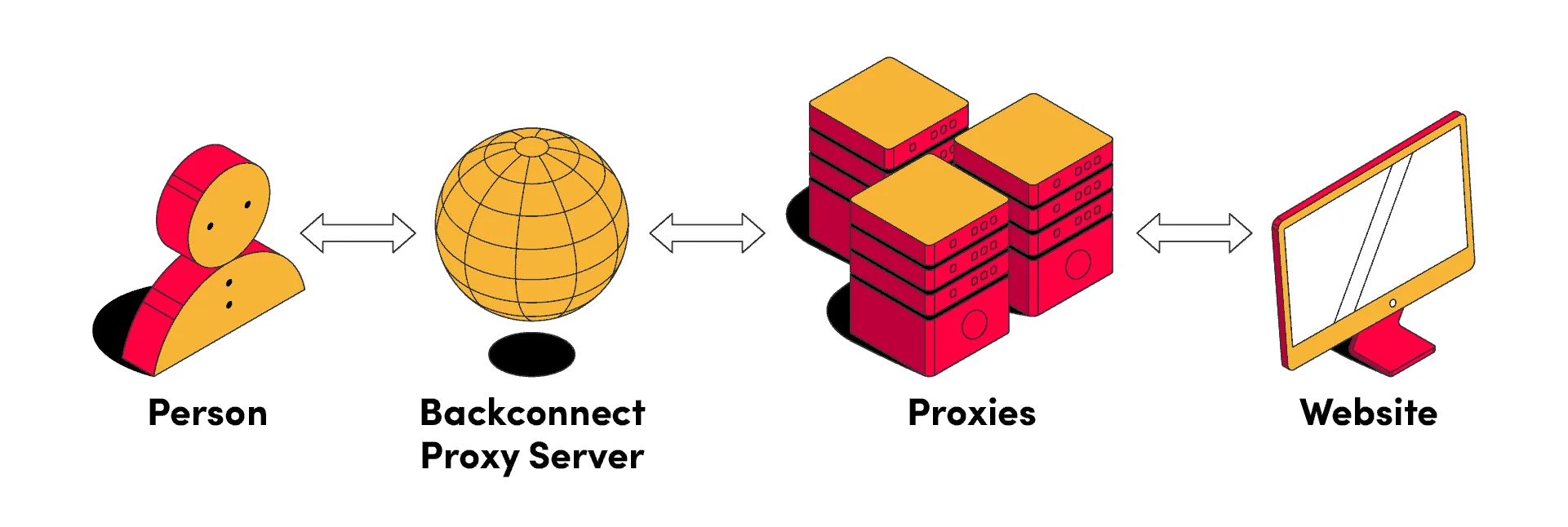
Backconnect proxy services, also called reverse proxies, represent a step toward better optimization of web workflows. They route outbound traffic through a single gateway that continuously cycles IP addresses from a large rotating residential or mobile pool. As a result, they make large-scale automation practical and sustainable, or conversely, protect websites from potential traffic overloads.
TL;DR
Backconnect (reverse rotating) proxies route all outbound traffic through a single gateway while continuously cycling IPs from a massive residential or mobile pool. CyberYozh offers a 50M+ residential network with city-level geotargeting, IP quality checks, and API-driven automation on that foundation.
A reverse proxy rotates IP addresses per request or per session, hiding your origin infrastructure from the target server, while forward proxies filter client-side traffic
They handle operations at scale: data scraping, account management, cybersecurity, and more
IP quality checks via CyberYozh's IP Checker screen for fraud score, blacklists, and anonymity leaks before each session
City-level geotargeting keeps sessions locally authentic for SERP tracking, ad verification, and account management
Key use cases include data scraping, bulk account management, crypto/Web3 automation, and server-side cybersecurity protection
What is a reverse proxy
A reverse (or backconnect) proxy is a server that acts as an intermediary between the requester and the destination, routing requests through a continuously rotating pool of IP addresses so each one appears to originate from a different location. For enterprises and web servers, it’s a critical infrastructure layer that enables traffic distribution, anonymization, and request-level control at scale.
Explore the best IP rotation proxy services in CyberYozh’s dedicated article.
Forward vs reverse proxy: Differences
These two proxy types are often confused but serve fundamentally different roles.
A forward proxy sits on the client side and filters outbound traffic. Companies use it to route corporate browsing through a single monitored exit point, while individuals can deploy it to protect their traffic.
A reverse proxy, by contrast, operates at the requester or server level: it intercepts outbound requests and distributes them across a pool of rotating IP addresses, masking the origin and making every interaction appear to come from a different organic user.
For scraping, multi-account operations, bulk automation, and server security, the reverse model delivers a higher operational value.
Aspect | Forward Proxy | Reverse Proxy |
Position | Sits between client and internet | Sits between server and target |
Who is hidden | Hides the client IP from external sites | Hides the origin infrastructure or requester |
Typical user | Corporate IT, individuals seeking privacy | Enterprises, scraping teams, automation operators |
IP behavior | Single IP or fixed list of outbound IPs | Rotates IPs per request or per sticky session |
Primary use case | Content filtering, secure browsing, small-scale activities | Scraping, account management, bulk automation |
Automation with backconnect proxies
One of the most compelling advantages of reverse rotating proxies is their ability to leverage massive IP pools to automate large-scale operations without interruption.
Learn about web scraping automation and explore how to use web scrapers in the best way.
It includes:
Pricing data collection from large platforms
Ad placements verification across dozens of regions
Managing hundreds of accounts simultaneously
A single IP or a small static pool will get blocked within minutes due to rate limits being exceeded and website overload. Backconnect proxies eliminate this bottleneck by distributing requests across millions of addresses, allowing workflows to run continuously, quietly, and at the required velocity. Rate limits or pattern-based detection aren’t triggered, as each individual IP operates within limits.
This said, a simple rotation isn’t enough. Random rotation, sticky sessions, and one IP per request are used for different use cases, and misusing them can lead to escalating issues. Explore IP rotation strategies on CyberYozh to select the best one for a specific task.
Setting up CyberYozh’s backconnect residential proxies
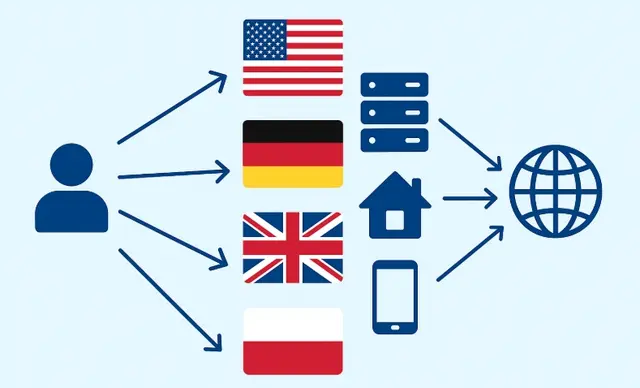
CyberYozh offers access to a residential IP pool of over 50 million IP addresses across 100+ countries, making it one of the most geographically diverse backconnect services. Getting started takes just a few minutes:
Sign up, then select a residential proxy plan in your account.
Configure your parameters by choosing a target country, city (if needed), rotation mode (per-request or sticky session), and protocol (HTTP or SOCKS5).
Retrieve your credentials: host, port, username, and password are generated automatically in your dashboard.
Connect your client: paste the credentials into your scraping tool, proxy manager, or an antidetect browser such as GoLogin or Undetectable, and you're ready to run.
Once configured, the infrastructure provides two additional operational layers: IP quality verification and precise geotargeting. Let’s see how they help.
Automation and IP quality checks
Before routing any request through a new IP, it's worth knowing what that address will look like to the target site and how it may react.
❓Click to know more
Every IP address has a usage history. Actually, that’s why IPv4 addresses are still widely used: they serve as digital passports, indicating to platforms whether the request's origin is trustworthy. Every action that may harm a website (such as request rate limit breaches) or its users (such as scams or spam) is recorded and, eventually, may reduce the IP’s trust score, leading to the IP being treated as more suspicious. Datacenter IPs usually have the lowest trust score, as they’re associated with bots, and mobile IPs have the highest.
CyberYozh's IP Checker handles exactly that. It evaluates the trust score of each address, so you can filter out risky IPs before they get you banned.
Fraud score screening identifies IPs linked to spam, bots, or abusive patterns before you use them for account operations or form submissions.
Blacklist and reputation lookup checks whether an IP appears on major blocklists, ensuring clean residential exits when working with high-trust platforms like marketplaces or payment processors.
Anonymity and leakage detection verifies that WebRTC, DNS, and other fingerprinting vectors don't expose your real connection behind the proxy layer.
For teams running fully automated pipelines, CyberYozh API lets you integrate these checks programmatically:
Pulling a fresh IP from the IP pool
Running it through the IP Checker
Rotating to it if the IP’s trust score is high enough
Therefore, it’s possible to assign a guaranteed clean IP to the next active session without any manual intervention.
Learn more about the proxy management cycle to understand how its quality is measured and applied.
Precise geotargeting for local activities
CyberYozh's geotargeting goes beyond country-level selection, offering city-level precision across its global residential pool. You can target a specific metropolitan area, for example, London, Chicago, Berlin, or Krakow, and ensure every request in a session appears to originate from that exact location.
Learn more about geotargeting and its specifics in CyberYozh’s dedicated article.
To configure it, simply select the target country and city in your dashboard, or pass country and city parameters through the API for programmatic control. Practical use cases include:
Local SERP tracking includes monitoring how a page ranks in a specific city without triggering location-based redirects or personalized results.
Ad verification requires confirming that geo-targeted campaigns render correctly for the intended regional audience.
Price monitoring is checking how e-commerce sites adjust pricing or product availability in local markets or exploring local promos.
Account management includes keeping sessions consistent with an account's registered location to prevent suspicious login alerts.
In each case, city-level targeting reduces false positives and makes automated sessions significantly more convincing to modern detection systems of local services.
Use cases of backconnect rotating proxies
Reverse rotating proxies are the operational backbone of many enterprise-grade web workflows, from market research to infrastructure security. Here's how specific teams use them to solve real problems at scale.
Large-scale data scraping
When a market research firm needs to track 200,000 product listings daily across multiple retailers, sending requests based on a small IP list is not viable.
Backconnect proxies distribute those requests across a rotating pool of residential IPs, bypassing per-IP rate limits and bot-detection heuristics. Each request appears to come from a different organic user, which means cleaner data, fewer CAPTCHA, and no sudden infrastructure bans disrupting a 24-hour collection run.
Bulk account management
Social media teams, affiliate networks, and growth agencies often need to manage or warm up hundreds of accounts across platforms like Instagram, TikTok, or Facebook.
Reverse rotating proxies assign a unique or sticky residential IP to each account session, making every profile appear to operate from a distinct device and location. Combined with an antidetect browser, this is the standard setup for keeping accounts active and preventing cross-linking between profiles.
Crypto and Web3 activities
Blockchain developers and crypto enthusiasts use backconnect proxies to manage multiple wallets, interact with decentralized applications (dApps), and pull large volumes of on-chain data from RPC endpoints.
A rotating residential pool helps ensure that repeated wallet interactions or smart contract calls aren't flagged as automated, which is especially important during high-competition events like token launches or NFT mints.
Cybersecurity and web protection
On the server side, reverse proxies are a foundational element of enterprise security architecture. They sit in front of backend infrastructure, filtering incoming requests, absorbing traffic attacks, and inspecting connections before they reach origin servers.
Services like Cloudflare operate as reverse proxies at a global scale, intercepting HTTP traffic, enforcing WAF rules, and acting as a protective shield between the public internet and the underlying web server. Organizations of any size can implement the same principle by placing a reverse proxy layer at the network edge.
Conclusion: Efficient solution for web servers
Reverse rotating proxies have become an operational standard for modern web enterprises. For protecting backend infrastructure, scraping data at scale, managing multi-account workflows, or collecting blockchain analytics, they offer a flexible and scalable control layer. CyberYozh makes that layer accessible, with a 50M+ residential pool, city-level targeting, quality checks, and full API integration.
Explore CyberYozh proxy catalog and select the best solution for your needs.
